


Validate that you meet cybersecurity regulatory requirements.
Create consistency between Home & Field Office Cyber Programs.
Gain awareness and visiblity into Field Offices compliance.
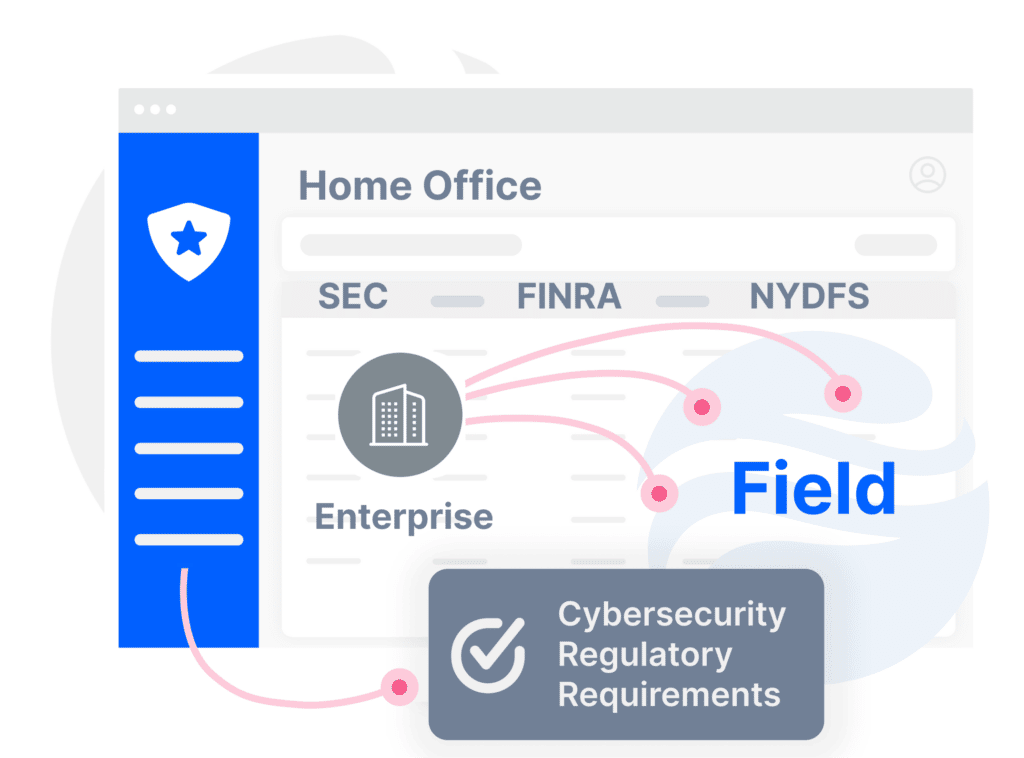
There are multiple laws, guidelines, risk alerts, and recommendations to follow.
For compliance, periodic tasks are monthly, quartlerly or yearly.
Tasks fall across a range of people and teams to ensure accountability.
It’s a mountain, not a hill to ensure full compliance and stay audit-ready.
Efficiently manage risk with policies grouped into 4 controls and multiple sections.
Use pre-defined policy titles and content to cover regulations you have to meet.
See the exact list of policies each Buckler policy matches across cybersecurity regulations.
Add specific details to policies to make them better reflect your environment.
Select who is responsible to define policies, who enforces them, and to whom they apply.
Define task frequency and get email reminders to never miss a deadline.
Monitor policy status: Active, draft, inactive, and to review. You can also add your own statuses.
Track everything you do for stronger evidence with a customizable log system.

“The simplicity and accuracy of Buckler policies are second to none.”
